Microsoft has admitted that it signed a driver that is actually a Rootkit. Security researchers have observed the rogue driver sending data and communicating with a Chinese company with alleged links to the Chinese military.
Microsoft has confirmed signing a malicious driver. Apparently, the driver was receiving instructions from a company that U.S. security officials believe is a front for the Chinese Military.
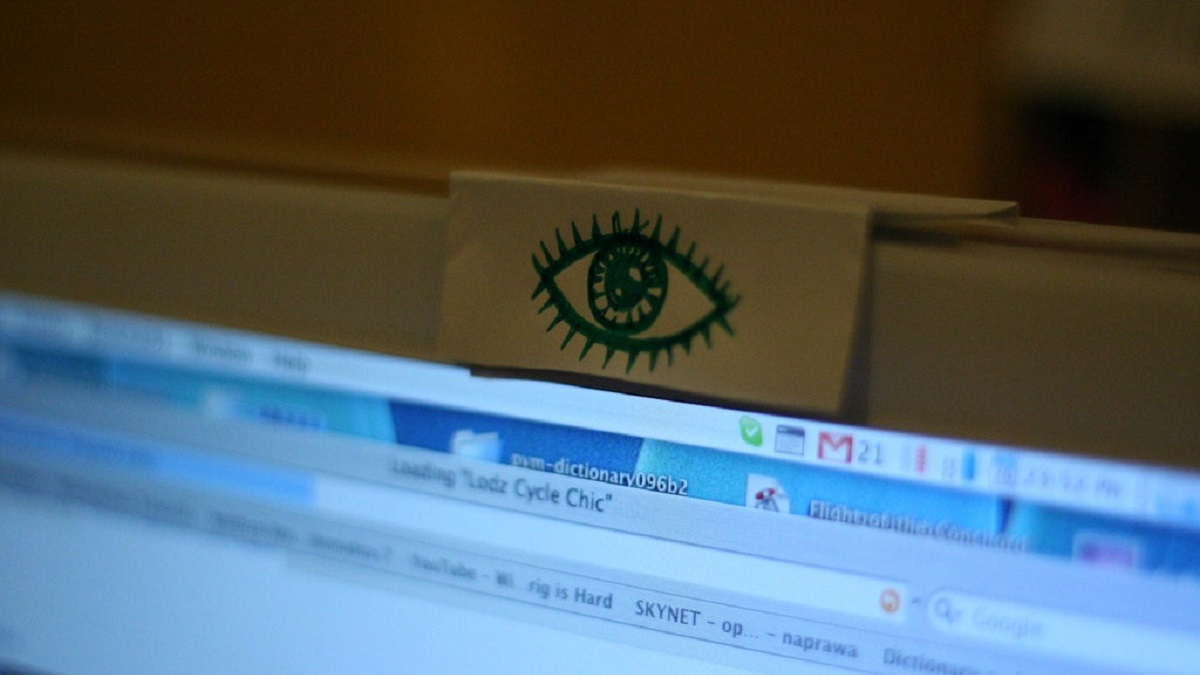
Microsoft itself signed a driver that turned out to be a low-level but effective espionage conduit:
Microsoft has confirmed that it signed a driver for general public distribution that was a rootkit in disguise. The company had mandated the practice of signing drivers since Windows Vista.
Microsoft signed a malicious Netfilter rootkit https://t.co/f8LtF3vUGL
— Matthew (@MathWebEntry) June 26, 2021
Since 2007, Microsoft has enforced the rule that Windows drivers must carry digital signatures by default. In fact, any piece of software that accesses the Windows Kernel or interacts with the core of the operating system must have a digital signature that Microsoft provides.
Now, G DATA Software security analyst Karsten Hahn has confirmed that a driver Microsoft digitally signed, was redirecting traffic bound for hundreds of IP addresses, to a server in China.
☢️Network filter rootkit that connects to this IP in China:
hxxp://110.42.4.180:2081/uIt does not look like Moriya (signature will be corrected asap)
File is signed by Microsoft.#rootkit #netfilterhttps://t.co/lhvmmgHn6w
— Karsten Hahn (@struppigel) June 17, 2021
Hahn collaborated with a few members of the Information Security (Infosec) community to trace and analyze the malicious driver that had the official seal of Microsoft. In essence, it appears skilled, and presumably, well-funded hackers exploited Microsoft’s code-signing process.
It is not immediately clear how the rogue driver, which was a rootkit, made it through Microsoft’s digital signature process. Needless to mention, Microsoft has launched an internal investigation to ascertain the facts. The company has reportedly offered an official statement:
“Microsoft is investigating a malicious actor distributing malicious drivers within gaming environments. The actor submitted drivers for certification through the Windows Hardware Compatibility Program. The drivers were built by a third party. We have suspended the account and reviewed their submissions for additional signs of malware.”
Spent some more time analyzing the Chinese netfilter driver discovered by @struppigel:
The core functionality seems to be eavesdropping on SSL connections. In addition to the IP redirecting component, it also installs (and protects) a root certificate to the registry.
— Johann Aydinbas (@jaydinbas) June 19, 2021
Incidentally, the widespread Stuxnet attack had used a similar rogue driver. The Stuxnet virus had drivers that belonged to Realtek, and malicious code writers had stolen the same.
Netfilter is a rootkit being distributed within gaming environments as a Microsoft-signed driver:
Reports indicate the owner of the rogue driver with the hidden rootkit is Ningbo Zhuo Zhi Innovation Network Technology Co., Ltd. The United States Department of Defense claims the company is a front for the Chinese military.
Microsoft signed the driver when it arrived as ‘Netfilter’. As part of the rootkit’s operational directives, it was communicating with China-based C&C Ips. There was no legitimate functionality or reasons for such activities, and hence, the driver raised suspicion.
.@FortiGuardLabs Threat Signal Report: NetFilter – Rootkit Signed with a Valid Digital Certificate https://t.co/j1RneYLJtn pic.twitter.com/Qa3g7FU7Ln
— Gernot Schauer (@morsella99) June 26, 2021
As Microsoft indicated in its statement, the creators of the rootkit aimed the rogue driver at gamers. Although still speculation, it appears the Chinese administration could be trying to spy on its own citizenry, particularly the gaming community.
Microsoft has indicated that there is no impact on the enterprise environments. Simply put, the rogue driver with the rootkit did not attempt to penetrate or spy on companies with sensitive or confidential data.
Despite no immediate threats to corporations, recent ransomware attacks are a grim reminder about the risks. And when Microsoft’s own security processes are exploited, the core reliability could be impacted.


